2023 CrowdStrike Global Threat Report Reveals Sophisticated Adversaries Re-exploiting and Re-weaponizing Patched Vulnerabilities and Moving Beyond Ransomware
CrowdStrike (CRWD) has released its 2023 Global Threat Report, highlighting significant trends in cybersecurity threats. The report identifies a 71% increase in malware-free attacks and notes a 112% rise in access broker ads on the dark web. Notably, cloud exploitation incidents surged 95%, with 'cloud-conscious' threat actors tripling in number.
Additionally, 33 new adversaries were identified, marking the highest increase in a year. The average breakout time for eCrime actors is now 84 minutes, down from 98 minutes in 2021. The report underscores escalating risks, particularly from China and eCrime groups.
- 71% of attacks detected were malware-free, indicating evolving threat sophistication.
- 112% year-over-year increase in access broker advertisements on the dark web demonstrates high demand for identity credentials.
- Cloud exploitation grew by 95%, highlighting increased targeting of cloud environments.
- 33 new adversaries identified, the largest annual increase ever recorded by CrowdStrike.
- Average eCrime breakout time decreased to 84 minutes, showing faster attack execution.
- Adversaries are increasingly re-weaponizing known vulnerabilities, complicating security efforts.
- The cyber impact of the Russia-Ukraine conflict is noted as significant, with increased espionage incidents.
Insights
Analyzing...
Emerging threat actors and increasing
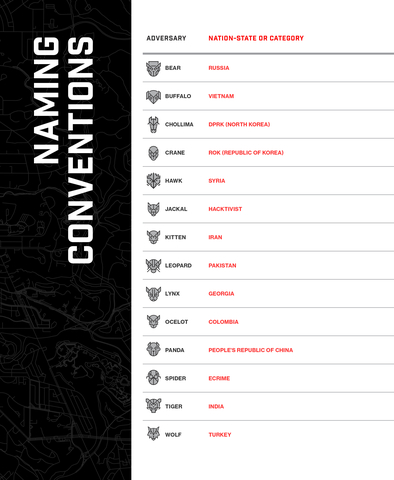
CrowdStrike Adversary Naming Conventions (Graphic: Business Wire)
The annual report is created by the world-renowned CrowdStrike Intelligence team, leveraging data from trillions of daily events from the CrowdStrike Falcon platform and insights from CrowdStrike Falcon OverWatch. Key highlights from this year’s report include:
-
71% of attacks detected were malware-free (up from62% in 2021) and interactive intrusions (hands on keyboard activity) increased50% in 2022 – Outlining how sophisticated human adversaries increasingly look to evade antivirus protection and outsmart machine-only defenses. -
112% year-over-year increase in access broker advertisements on the dark web – Illustrating the value of and demand for identity and access credentials in the underground economy. -
Cloud exploitation grew by
95% and the number of cases involving ‘cloud-conscious’ threat actors nearly tripled year-over-year – More evidence adversaries are increasingly targeting cloud environments. -
33 new adversaries introduced – The biggest increase
CrowdStrike has ever observed in one year – including the highly prolific SCATTERED SPIDER and SLIPPY SPIDER behind many recent high-profile attacks on telecommunication, BPO, and technology companies. - Adversaries are re-weaponizing and re-exploiting vulnerabilities – Spilling over from the end of 2021, Log4Shell continued to ravage the internet, while both known and new vulnerabilities like ProxyNotShell and Follina – just two of the more than 900 vulnerabilities and 30 zero-days Microsoft issued patches for in 2022 – were broadly exploited as nation-nexus and eCrime adversaries circumvented patches and side stepped mitigations.
-
eCrime actors moving beyond ransom payments for monetization – 2022 saw a
20% increase in the number of adversaries conducting data theft and extortion campaigns. -
China -nexus espionage surged across all 39 global industry sectors and 20 geographic regions tracked by CrowdStrike Intelligence – Rise inChina -nexus adversary activity shows that organizations across the world and in every vertical must be vigilant against the threat fromBeijing . - Average eCrime breakout time is now 84 minutes – This is down from 98 minutes in 2021, demonstrating the extensive speed of today’s threat actors.
-
The cyber impact of
Russia -Ukraine war was overhyped but not insignificant –CrowdStrike saw a jump inRussia -nexus adversaries employing intelligence gathering tactics and even fake ransomware, suggesting the Kremlin’s intent to widen targeting sectors and regions where destructive operations are considered politically risky. - An uptick in social engineering tactics targeting human interactions – Tactics such as vishing direct victims to download malware and SIM swapping to circumvent multifactor authentication (MFA).
“The past 12 months brought a unique combination of threats to the forefront of security. Splintered eCrime groups re-emerged with greater sophistication, relentless threat actors sidestepped patched or mitigated vulnerabilities, and the feared threats of the
A closer look at some of the new adversaries:
CrowdStrike Intelligence added 33 newly tracked adversaries bringing the total number of known adversaries tracked to more than 200. More than 20 of the new additions were SPIDERS, the
The CrowdStrike Intelligence team benefits from an unparalleled raw collection of intelligence data, leveraging trillions of security events per day to help stop the most ubiquitous of threats and power the CrowdStrike Falcon® platform. As the platform of consolidation in security, Falcon enables organizations to proactively stop the most sophisticated of threats via its unique combination of endpoint and identity threat protection technology, adversary-driven intelligence and human-led analysis.
Additional Resources
- Download the 2023 CrowdStrike Global Threat Report.
- Visit CrowdStrike’s Adversary Universe for the internet’s definitive source on adversaries.
- To learn more about integrating threat intelligence into your security stack with CrowdStrike’s industry-leading, adversary-focused technology, please visit our website.
About
Powered by the CrowdStrike Security Cloud and world-class AI, the CrowdStrike Falcon® platform leverages real-time indicators of attack, threat intelligence, evolving adversary tradecraft and enriched telemetry from across the enterprise to deliver hyper-accurate detections, automated protection and remediation, elite threat hunting and prioritized observability of vulnerabilities.
Purpose-built in the cloud with a single lightweight-agent architecture, the Falcon platform delivers rapid and scalable deployment, superior protection and performance, reduced complexity and immediate time-to-value.
Learn more: https://www.crowdstrike.com/
Follow us: Blog | Twitter | LinkedIn | Facebook | Instagram
Start a free trial today: https://www.crowdstrike.com/free-trial-guide/
© 2023
View source version on businesswire.com: https://www.businesswire.com/news/home/20230228005546/en/
press@crowdstrike.com
Source:







